SBOM Explained: Why a Software Bill of Materials Is Now a Cybersecurity Must
Modern software is rarely built from scratch. Today, apps are made up of hundreds or even thousands of third-party libraries, open-source components and dependencies. This speeds up development, but it also leaves a big security gap: a lot of companies don’t know exactly what’s in the software they use.
This risk is impossible to ignore because of the high-profile supply chain attacks. Even if their own code is safe, organisations can be at risk if third-party components have security gaps that are hard to find. This is why using SBOM has gone from being a niche best practice to a must-have for cybersecurity.
Understanding what an SBOM is, how a software bill of materials works, and why it matters is now important for security leaders, developers and compliance teams alike.
What is an SBOM?
A Software Bill of Materials (SBOM) is a formal, organised list of all the components that make up a software product. It shows how software is built by listing libraries, frameworks, dependencies, and their versions.
A typical software bill of materials has:
- Component names and versions
- Relationships of dependence
- Information about licenses
- Information about the supplier or origin
- Cryptographic hashes for integrity
This transparency helps businesses better understand and deal with software risk.
Why SBOMs Are So Important for Online Safety
The risk of software supply chains is much higher because they are becoming more complicated.
SBOMs are now necessary because they help businesses:
- Find weaknesses quickly
- React faster to newly found weaknesses
- Get rid of blind spots in the supply chain
- Improve trust in third-party software
- Improve overall risk management
Without an SBOM, companies often have a hard time figuring out if they are affected by a vulnerability. This wastes valuable time during incidents.
How SBOMs Improve Software Supply Chain Visibility
Security teams can’t protect what they can’t see.
An SBOM improves visibility by:
- Giving a full list of dependencies
- Showing indirect or transitive parts
- Pointing out outdated or unsupported libraries
- Faster impact analysis during vulnerability disclosures
This level of insight makes the software bill of materials a foundational control of modern application security.
SBOM and Vulnerability Management
SBOMs play a big role in strengthening vulnerability management processes.
When a new vulnerability is disclosed, an SBOM allows teams to:
- Find the affected parts quickly
- Determine which apps are affected
- Prioritise remediation in order of exposure
- Reduce manual investigation effort
This ability speeds up response times and reduces operational chaos during high-risk disclosures.
Regulatory and Compliance Drivers for SBOM Adoption
Regulatory expectations are becoming a big reason for people to use SBOM.
A lot of standards and frameworks now suggest or require SBOMs to:
- Make software more transparent
- Make the supply chain safer
- Support compliance methods based on risk
The SBOM is becoming a practical requirement instead of an optional control as regulators pay more attention to supply chain security.
Common SBOM Formats and Standards
SBOMs need to follow standard formats to work.
Some common SBOM formats are:
- SPDX (Software Package Data Exchange)
- CycloneDX
- SWID (Software Identification Tags)
These formats make it possible to share, parse and add SBOMs to security tools, which makes the software bill of materials useful on a large scale.
How Organisations Generate and Maintain SBOMs
Creating an SBOM is not a one-time activity. It must change with the software.
Most of the time, organisations make SBOMs by:
- Integrating SBOM generation to CI/CD pipelines
- Using tools to scan for dependencies
- Updating SBOMs automatically with every release
- Checking the integrity and versions of components
Keeping an SBOM up to date makes sure that visibility stays accurate as software changes.
Challenges Organisations Face with SBOM Implementation
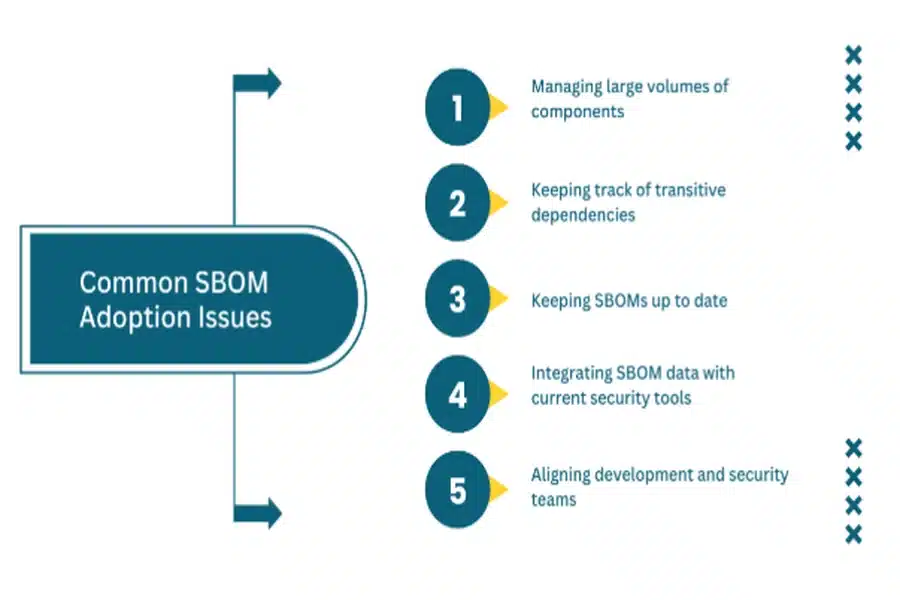
Adopting SBOM is useful, but it also comes with certain drawbacks.
Some common problems are:
- Managing large volumes of components
- Keeping track of transitive dependencies
- Keeping SBOMs up to date
- Integrating SBOM data with current security tools
- Aligning development and security teams
To deal with these problems, you need to align and automate your processes.
SBOMs And Third-Party Risk Management
One of the biggest risks in modern environments comes from third-party software.
A software bill of materials helps manage third-party risk by:
- Providing transparency into vendor software components
- Enabling faster vendor risk assessments
- Helping people make smart buying choices
- Improving incident response coordination with suppliers
This means that SBOMs are useful for more than just internal development teams.
When Organisations Should Prioritise SBOM Adoption
SBOM adoption is especially important for organisations that:
- Develop or distribute software products
- Rely heavily on open-source components
- Operate in regulated industries
- Manage complex application portfolios
- Face high supply chain exposure
In these scenarios, the SBOM becomes a core cybersecurity capability.
Next Steps
Organisations looking to strengthen software supply chain security should start by assessing their current visibility into application components. Identifying where dependencies are unknown or unmanaged is the first step toward SBOM adoption.
A structured approach to implementing a software bill of materials includes standardising formats, automating generation, and integrating SBOM data into vulnerability management workflows. CyberNX is a cybersecurity firm that helps organisations strengthen their SBOM management through their in-house built SBOM management tool which delivers deep component insights, automates vulnerability detection and does compliance tracking across your entire software supply chain.
Companies can become more transparent and resilient by including SBOMs in their development and security processes.
Conclusion
Software supply chain attacks have shown that hidden dependencies are a real and immediate threat. An SBOM gives you the information you need to know about what software is made of and how vulnerabilities could affect a business.
As cybersecurity threats change, the software bill of materials has become an important tool for managing risk, improving response times and building trust in software. For businesses that care about modern cybersecurity, using SBOM is no longer a choice; it is necessary.



